Categories
All
What Is Doxxing and What to Do If You’ve Been Doxxed
With the amount of information now living online, it’s not hard to see why so many people are falling victim to doxxing. What’s more, platforms such as social media have made this issue much worse, as what can start as an online dispute, is blown totally out of proportion. The effects of doxing can permanently…
All
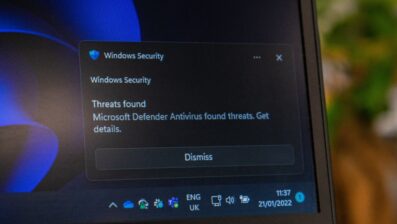
What Is a Ransomware Attack and How Does It Work?
For you to protect the important and confidential data within your organisation, it’s important to understand how ransomware attacks work. Ransomware is one of the most prominent and visible types of malware circulating the online world, and can result in loss of files, data, company funds, and in extreme cases bankruptcy. As with any form…
All
How to Draft an Incident Response Policy: What to Include
If your company were to be hit by a cyber attack, do you have an incident response plan in place? Would all members in your organisation know how to respond and what protocols to follow? Or would this create panic as everyone scrambles to get the situation under control? Unfortunately with the amount of information…

All
What Does Phishing Mean and How to Prevent It
What does phishing mean exactly? This is a popular question, one asked by hundreds if not thousands of individuals at all levels of an organization – from entry level positions all the way up to business owners. The popularity of this query comes down to two factors: How flexible this type of attack is How…

All
What Is SSO and How Does it Work?
The chances are, you have logged into something through single sign-on this week, but are still wondering ‘what is SSO and how does it work?’ Or better still, ‘why should my business use SSO?’ Well keep reading, this blog has the answers. When it comes to your business, having a strong security system in place…

All
What is A Rootkit: How to Detect and Prevent It
Understanding the answer to ‘what is a rootkit’ is very important if you work in an organization prone to cyber attacks. For those unfamiliar with this type of malware, rootkits are used by hackers to access and take control over a targeted device. Rootkits are very effective at concealing their presence while remaining active, which…

All
7 Different Hacker Examples: Motives, Aims, and What That Means For Your Business
For the safety of your organisation it’s essential to understand the attributes of the 7 different hacker examples. Some hackers will protect you, while others will use viruses and malware with malicious intent, to steal your data, or for financial gain. These hackers typically find loopholes and vulnerabilities within your network before they strike, and…
All
What Is A Cyber Security Strategy and How Can I Develop My Own?
Creating and implementing a cyber security strategy takes careful consideration, but could be the difference between successfully fending off cyber threat actors, and losing important company data. Failing to align your company goals, cyber security architecture, and your strategy could result in gaps in your network, and therefore allow a way for attackers to penetrate…

All
What Is a White Hat Hacker and What Do They Do?
‘What is a white hat hacker’ is a confusing question to someone not up to date with their cybersecurity terminology. The same might apply if we were to ask you how extensive your knowledge is of black hat and gray hat hackers (the other two members of this unique trio). While important, our main focus…