What Is Artificial Intelligence and How Does it Affect Cyber Security?
All
As cyber security expands, more and more companies are asking themselves “what is artificial intelligence and should we be using it?”
Ultimately, AI can benefit both smaller and larger organisations by improving cyber security measures, as well as improving day-to-day operations and processes.
However, if AI machines fall into the wrong hand,s it’s possible that cyber threat actors can use the technology and information to conduct more complex attacks
Therefore, it’s essential to understand how machine learning can negatively or positively affect your company’s network.
In this post we will be exploring the 4 types of AI, how they work, and their direct effect on cyber security, whether that be strengthening systems or allowing hackers to conduct more complex attacks.
What Is Artificial Intelligence?
Artificial Intelligence or AI, is the simulation of human intelligence processes by machines.
In other words, AI is a wide-ranging branch of computer science that is concerned with building smart machines that are capable of performing tasks that typically require human intelligence.
Artificial intelligence allows machines to model the capabilities of the human mind and build upon them, for example, the likes of self-driving cars and Alexa and Siri responding to commands and questions.
As AI continues to grow, more companies are beginning to use smart machines internally to provide insight into their operations and processes that they may not have considered or accessed before.
In some cases, AI can perform tasks to a higher standard than humans, particularly when it comes to detail-oriented tasks that are sometimes repetitive. For example, ensuring fields are filled with relevant data in a spreadsheet or a large table as this is quite monotonous.
For tasks such as these, AI tools often complete tasks much faster and with very few or no errors at all.
The 4 Types of AI
As Artificial Intelligence is constantly expanding, it has been split into 4 categories based on the type, complexity, and the kind of tasks it can be used for.
Whilst two of these groups haven’t yet been created, there is a version mapped-out for them in the future, so let’s take a look!’
Reactive Machines
Reactive machines are the most basic of AI principles as they use the intelligence they have to perceive and react to the world around them.
However, these machines do not store memory and therefore can’t use past experience or information they have received to make decisions in the present.
This may be seen as a slight drawback, however, this makes reactive machines trustworthy and reliable as they will react in the same way each time they are asked a question or view a specific interaction.
Unlike the more advanced AI machines (and humans for that matter), reactive machines cannot change their minds based on experiences.
Limited Memory Machines
The next step up in AI from reactive machines is limited memory machines, which have the ability to store previous data and predictions.
This allows machines to use past data as clues to help them come to decisions, meaning they are more complex and present greater opportunities.
These limited memory machines are created when a team continuously trains a model in how to analyse and utilise new data, or an AI environment is built so models can be automatically trained.
Theory of Mind
As the name suggests, this example of AI is still just a theory and has not yet been achieved.
The premise of this type of Artificial Intelligence is the creation of a machine that has a psychological understanding that other living things have thoughts and emotions that have an effect on behaviour.
Essentially this type of AI means that researchers will need to create machines that understand how humans, animals, and even other machines feel and make decisions.
As a result, these machines must grasp the challenging concept of the mind.
Self-Awareness
Finally, self-awareness is a concept that will be born far into the future of AI, and this is the process of machines becoming completely self-aware.
This requires AI machines to possess a human level of consciousness, understanding its presence as well as emotions and the presence of others.
Essentially, this means machines will become much more similar to humans, and this relies on researchers understanding the state of consciousness and being, and replicating this in machines.
For example, when communicating in a customer service live chat on a company website, it will be almost impossible to determine whether you are in conversation with a human or an artificially intelligent machine.
How Does AI Work?
Artificial Intelligence requires a foundation of specialised hardware and software for writing and training machine learning algorithms.
At a basic level, AI systems work by ingesting large amounts of data, which they can then analyse for patterns in order to make predictions.
For example, a chatbot will be fed various examples of text chats so that it can learn to produce lifelike conversations with others.
When training AI systems there is a centralised focus on 3 processes: learning, reasoning, and self-correction, in order for machines to work as a human would.
Let’s take a look at these processes in more depth:
- Learning – this process is focused on acquiring data and creating rules around them on how to turn data into actionable information.
- Reasoning – the reasoning process focuses on choosing the right algorithm to reach the desired outcome.
- Self-correction – this process ensures that machines are continually fine-tuning algorithms to provide the most accurate results and responses at all times.
How Does AI Affect Cyber Security?
Artificial Intelligence has both advantages and disadvantages when it comes to cyber security.
While organisations can use the latest AI tools to detect threats more efficiently, cyber criminals can use the technology to launch more complex and sophisticated attacks.
Advantages of Using AI for Cyber Security
Across the globe, AI is already being used for various elements of cyber security including:
- Fraud detection
- Spam filter applications
- Botnet detection
- Secure user authentication
- Network intrusion detection and prevention
However, AI and machine learning can be used more generally across the board in order to build stronger security architectures and detect new and evolving viruses.
Easier to Build Defenses
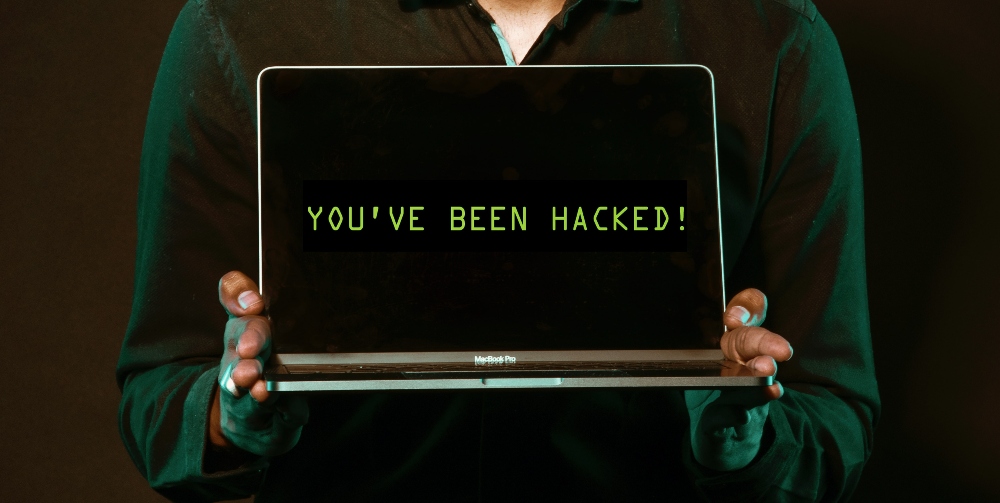
In previous years, hackers were skilled and used coding to hack into networks and devices without the help of software or AI, however, it’s now much simpler to conduct an attack thanks to creation of malware and new intelligence.
Currently, malware can be sold as something simple to plug into a device and get to work, meaning the process of hacking no longer requires experts.
Unfortunately, this means there is a higher volume of attacks, as anyone with a motive and the means to purchase malware can hack into networks and compromise company data.
In order to remedy this, an intelligent solution is needed which is where AI can be useful and used as a monitoring tool.
This involves using these machines as vulnerability scanners in order to identify problems quickly based on analysis of behaviour, recognise patterns, and react accordingly.
Ultimately, AI machines can detect and eliminate hackers far quicker than humanly possible as these models can ingest data from a company, get an idea of the baseline of activity, and it will automatically flag up when something suspicious or unusual happens.
Boost Biometric Authentication
Equally, a large pain point for many device users across different organisations is choosing, using, and changing passwords for accounts to ensure security.
This has been infiltrated by hackers using social engineering attacks and password attacks in order to steal or compromise data.
Artificial Intelligence can help with this issue, as the use of biometric logins, such as fingerprint, retina, or palm scanning can be used as an extra layer of protection between the user or hacker and the information within a device or account.
Users will be required to register their personal fingerprint or eye in order to use this login method, and this consequently creates a barrier for hackers as they will be unable to access biometric login information.
These biometric login methods can be used alone or in conjunction with a password, so can act as a singular credential or another layer of authentication to ensure the safety of a user’s account.
Machine Learning Can Detect Evolving Malware
Machine learning can be used to identify risks quickly and effectively as the speed of AI surpasses the speed of traditional human approaches.
A malware database with machine learning through AI can identify malware, whether it’s tweaked or existing, and block it from accessing a network or company systems based on previous behaviour or actions.
Ultimately, AI systems can be trained to detect ransomware of all kinds before they gain entry into a system.
Drawbacks to Using AI for Cyber Security
Although AI can be a positive for organisations in many senses, for example, protecting your network and systems by scanning for vulnerabilities or securing logins, it can be harmful when in the wrong hands.
Cyber criminals can use Artificial Intelligence to strengthen their cyber attacks and create pathways into a network that are more complex and sophisticated.
Equally, AI is not an option that is suited to or available to all companies, so it’s important to consider all of the options out there.
Machine Learning Can Help to Improve Attacks
Firstly, machine learning can be useful for hackers to learn from each attack that they conduct.
Cyber attackers can attach AI to their programming in order to watch the way they use malware to gain access to a network and adapt their processes accordingly.
Whether that be to increase efficiency and speed, or implement new strategies or malware to increase the success of the attacks they conduct.
For example, hackers may use elements of Artificial Intelligence to mimic human or trusted activity in order to trick their way into a network.
Therefore, AI can be extremely useful for criminals conducting a range of cyber attacks as machines can act as internal members of an organisation, colleagues, or clients in order to gain entry into a company network.
Implementing AI Systems is Expensive and Takes Time
In order to use AI within an organisation, it requires a significant increase in human and financial resources to both construct and manage an AI system.
To incorporate AI into your organisation, your company will need to obtain malware and non-malicious codes in order to train AI systems into utilising and recognising certain data sets.
As a result, this process can cost a lot and take up a lot of company time and not all companies can afford this.
Equally, AI systems can’t always be relied upon as they can provide incorrect data and get things wrong if they are handling too much data at once.
This means using Artificial Intelligence is not always a trustworthy option, and the training you conduct with individual machines may have the opposite effect.
What Is Artificial Intelligence and How Does it Affect Cyber Security?
Artificial Intelligence and machine learning can be highly valuable and useful for companies looking to improve their operations and processes, or their cyber security.
Although AI is always evolving and takes some of the pressure off your IT team, there are other methods that can support your company’s cyber security policies.
Here at TLR, we have a vulnerability scanning service that you can count on to identify weaknesses, analyse them, and exploit the weak security spots in your network.
This can be managed by us onsite or remotely, so your IT team can focus on the other important aspects of your cyber security policies without fear of any unexpected attacks.
If you feel your organisation could benefit from our services, get in touch with a member of our team today.


